Follow these steps to set up an Amazon Web Services account, create an IAM user, and configure access to CodeCommit.
To create and configure an IAM user for accessing CodeCommit
Note
If you want to use AWS CLI commands with CodeCommit, install the AWS CLI. For more information, see Command line reference.
To work with files, commits, and other information in CodeCommit repositories, you must install Git on your local machine. CodeCommit supports Git versions 1.7.9 and later. Git version 2.28 supports configuring the branch name for initial commits. We recommend using a recent version of Git.
To install Git, we recommend websites such as Git Downloads.Note
Git is an evolving, regularly updated platform. Occasionally, a feature change might affect the way it works with CodeCommit. If you encounter issues with a specific version of Git and CodeCommit, review the information in Troubleshooting.
If the version of Git you installed does not include a Bash emulator, such as Git Bash, install one. You use this emulator instead of the Windows command line when you configure SSH connections.
To set up the public and private keys for Git and CodeCommit on Windows
$ ssh-keygen Generating public/private rsa key pair. Enter file in which to save the key (/drive/Users/user-name/.ssh/id_rsa): Type a file name here, for example /c/Users/user-name/.ssh/codecommit_rsa Enter passphrase (empty for no passphrase): <Type a passphrase, and then press Enter> Enter same passphrase again: <Type the passphrase again, and then press Enter> Your identification has been saved in drive/Users/user-name/.ssh/codecommit_rsa. Your public key has been saved in drive/Users/user-name/.ssh/codecommit_rsa.pub. The key fingerprint is: 45:63:d5:99:0e:99:73:50:5e:d4:b3:2d:86:4a:2c:14 user-name@client-name The key's randomart image is: +--[ RSA 2048]----+ | E.+.o*.++| | .o .=.=o.| | . .. *. +| | ..o . +..| | So . . . | | . | | | | | | | +-----------------+This generates:codecommit_rsa file, which is the private key file.codecommit_rsa.pub file, which is the public key file.ssh-keygen -t rsa -b 4096For more information about the formats and lengths required for SSH keys, see Using IAM with CodeCommit.codecommit_rsa.pub):cd .ssh notepad codecommit_rsa.pubCopy the contents of the file, and then close Notepad without saving. The contents of the file look similar to the following:ssh-rsa EXAMPLE-AfICCQD6m7oRw0uXOjANBgkqhkiG9w0BAQUFADCBiDELMAkGA1UEBhMCVVMxCzAJB gNVBAgTAldBMRAwDgYDVQQHEwdTZWF0dGxlMQ8wDQYDVQQKEwZBbWF6b24xFDASBgNVBAsTC0lBTSBDb2 5zb2xlMRIwEAYDVQQDEwlUZXN0Q2lsYWMxHzAdBgkqhkiG9w0BCQEWEG5vb25lQGFtYXpvbi5jb20wHhc NMTEwNDI1MjA0NTIxWhcNMTIwNDI0MjA0NTIxWjCBiDELMAkGA1UEBhMCVVMxCzAJBgNVBAgTAldBMRAw DgYDVQQHEwdTZWF0dGxlMQ8wDQYDVQQKEwZBbWF6b24xFDAS=EXAMPLE user-name@computer-nameAPKAEIBAERJR2EXAMPLE).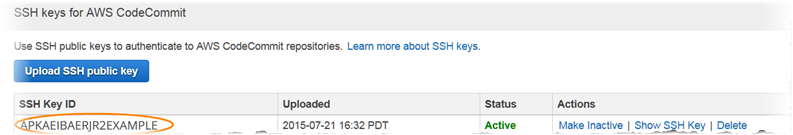 NoteIf you have more than one SSH key IDs uploaded, the keys are listed alphabetically by key ID, not by upload date. Make sure that you have copied the key ID that is associated with the correct upload date.
NoteIf you have more than one SSH key IDs uploaded, the keys are listed alphabetically by key ID, not by upload date. Make sure that you have copied the key ID that is associated with the correct upload date.notepad ~/.ssh/configUser is the SSH key ID you copied earlier, and the value for IdentityFile is the path to and name of the private key file:Host git-codecommit.*.amazonaws.com User APKAEIBAERJR2EXAMPLE IdentityFile ~/.ssh/codecommit_rsaNoteIf you gave your private key file a name other than codecommit_rsa, be sure to use it here.You can set up SSH access to repositories in multiple Amazon Web Services accounts, For more information, see Troubleshooting SSH connections to AWS CodeCommit.Save the file as config (not config.txt), and then close Notepad.ImportantThe name of the file must be config with no file extension. Otherwise, the SSH connections fail.ssh git-codecommit.us-east-2.amazonaws.comYou are asked to confirm the connection because git-codecommit.us-east-2.amazonaws.com is not yet included in your known hosts file. The CodeCommit server fingerprint is displayed as part of the verification (a9:6d:03:ed:08:42:21:be:06:e1:e0:2a:d1:75:31:5e for MD5 or 3lBlW2g5xn/NA2Ck6dyeJIrQOWvn7n8UEs56fG6ZIzQ for SHA256).NoteCodeCommit server fingerprints are unique for every AWS Region. To view the server fingerprints for an AWS Region, see Server fingerprints for CodeCommit.After you have confirmed the connection, you should see confirmation that you have added the server to your known hosts file and a successful connection message. If you do not see a success message, double-check that you saved the config file in the ~/.ssh directory of the IAM user you configured for access to CodeCommit, that the config file has no file extension (for example, it must not be named config.txt), and that you specified the correct private key file (codecommit_rsa, not codecommit_rsa.pub).To troubleshoot problems, run the ssh command with the -v parameter. For example:ssh -v git-codecommit.us-east-2.amazonaws.comFor information to help you troubleshoot connection problems, see Troubleshooting SSH connections to AWS CodeCommit.If an administrator has already sent you the name and connection details for the CodeCommit repository, you can skip this step and clone the repository directly.
To connect to a CodeCommit repository
MyDemoRepo to a local repo named my-demo-repo in the US East (Ohio) Region:git clone ssh://git-codecommit.us-east-2.amazonaws.com/v1/repos/MyDemoRepo my-demo-repoAlternatively, open a command prompt, and using the URL and the SSH key ID for the public key you uploaded to IAM, run the git clone command. The local repo is created in a subdirectory of the directory where you run the command. For example, to clone a repository named MyDemoRepo to a local repo named my-demo-repo:git clone ssh://Your-SSH-Key-ID@git-codecommit.us-east-2.amazonaws.com/v1/repos/MyDemoRepo my-demo-repoFor more information, see Connect to the CodeCommit repository by cloning the repository and Create a commit.You need to login in order to like this post: click here
YOU MIGHT ALSO LIKE